Recent GitHub supply chain attack traced to leaked SpotBugs token

A cascading supply chain attack on GitHub that targeted Coinbase in March has now been traced back to a single token stolen from a SpotBugs workflow, which allowed a threat actor to compromise multiple GitHub projects.
The popular static analysis tool SpotBugs was breached in November 2024, leading to the compromise of Reviewdog, which subsequently led to the infection of tj-actions/changed-files.
The multi-step supply chain attack eventually exposed secrets in 218 repositories, while the latest findings showed that the threat actors were initially attempting to breach projects belonging to the cryptocurrency exchange Coinbase.
The start of the attack, which has remained unknown so far, was discovered by Palo Alto Networks' Unit 42 researchers who added an update yesterday on their original analysis of the incident.
The cascading supply chain attack
We now know that the supply chain attack started in late November 2024 when a SpotBugs maintainer (SPTBHS_MNTNR) added their Personal Access Token (PAT) into a CI workflow.
On December 6, 2024, an attacker exploited a vulnerable 'pull_request_target' workflow to steal the maintainer's PAT via a malicious pull request from a throwaway user account (randolzflow).
On March 11, 2025, the attacker used the stolen PAT to invite another dummy user (jurkaofavak) into SpotBugs, who pushed a malicious GitHub Actions workflow that exfiltrated another PAT belonging to a Reviewdog maintainer (RD_MNTNR) who also had access to SpotBugs.
The stolen PAT had write access to 'reviewdog/action-setup,' allowing the attacker to override the v1 tag with a malicious commit from a fork, poisoning all consumers of v1.
This created a backdoor that was executed when used by 'tj-actions/eslint-changed-files,' which the project relied on.
Using stolen credentials, the attacker overrode git tags in the repository to point to a malicious commit that would dump secrets from CI runners into logs, potentially impacting 23,000 repositories using that action. However, it was later determined that the malicious tj-actions commit only exposed secrets for 218 repositories.
As revealed during post-incident investigations, the attacker tailored the malicious commit to target 'coinbase/agentkit.' Coinbase's CI pulled and executed the tainted version on March 14, 2025.
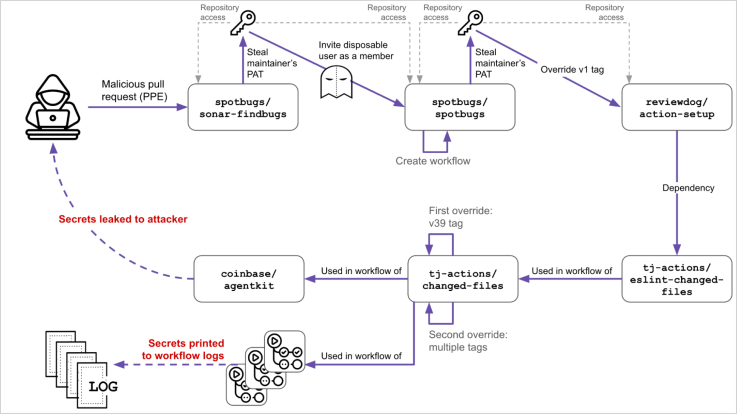
Despite this, no Coinbase secrets were exposed, so the attacker's attempt to access the exchange's infrastructure failed. The company was quickly tipped about the attempted breach and removed the workflow.
Now that the complete picture of the incident has been painted, it becomes clear that the breach was highly organized and meticulously planned, starting months earlier than initially known.
Also, the incident highlights fundamental problems in the chain of trust between open-source repositories, as well as GitHub Action ecosystem issues like tag mutability and poor audit logging.
Projects and repositories that used the compromised actions should rotate all secrets immediately.
GitHub Actions logs, especially those from March 10-14, 2025, should be audited for signs of secrets being printed, especially base64-encoded blobs.
To mitigate the risk of similar attacks in the future, it is recommended to pin dependencies using commit hashes instead of tags, and avoid 'pull_request_target' unless necessary.
Top 10 MITRE ATT&CK© Techniques Behind 93% of Attacks
Based on an analysis of 14M malicious actions, discover the top 10 MITRE ATT&CK techniques behind 93% of attacks and how to defend against them.
Lazarus Group Targets Job Seekers With ClickFix Tactic to Deploy GolangGhost Malware
Texas State Bar warns of data breach after INC ransomware claims attack
CVE-2024-20439 Cisco Smart Licensing Utility Static Credential Vulnerability
CVE-2025-2783 Google Chromium Mojo Sandbox Escape Vulnerability
CVE-2019-9874 Sitecore CMS and Experience Platform (XP) Deserialization Vulnerability
CVE-2019-9875 Sitecore CMS and Experience Platform (XP) Deserialization Vulnerability
CVE-2025-30154 reviewdog/action-setup GitHub Action Embedded Malicious Code Vulnerability
CVE-2025-1316 Edimax IC-7100 IP Camera OS Command Injection Vulnerability
CVE-2024-48248 NAKIVO Backup and Replication Absolute Path Traversal Vulnerability
CVE-2017-12637 SAP NetWeaver Directory Traversal Vulnerability
CVE-2025-24472 Fortinet FortiOS and FortiProxy Authentication Bypass Vulnerability
InformationalInformation Disclosure - Suspicious Comments
InformationalRe-examine Cache-control Directives
Free online web security scanner







