NachoVPN Tool Exploits Flaws in Popular VPN Clients for System Compromise

Cybersecurity researchers have disclosed a set of flaws impacting Palo Alto Networks and SonicWall virtual private network (VPN) clients that could be potentially exploited to gain remote code execution on Windows and macOS systems.
"By targeting the implicit trust VPN clients place in servers, attackers can manipulate client behaviours, execute arbitrary commands, and gain high levels of access with minimal effort," AmberWolf said in an analysis.
In a hypothetical attack scenario, this plays out in the form of a rogue VPN server that can trick the clients into downloading malicious updates that can cause unintended consequences.
The result of the investigation is a proof-of-concept (PoC) attack tool called NachoVPN that can simulate such VPN servers and exploit the vulnerabilities to achieve privileged code execution.
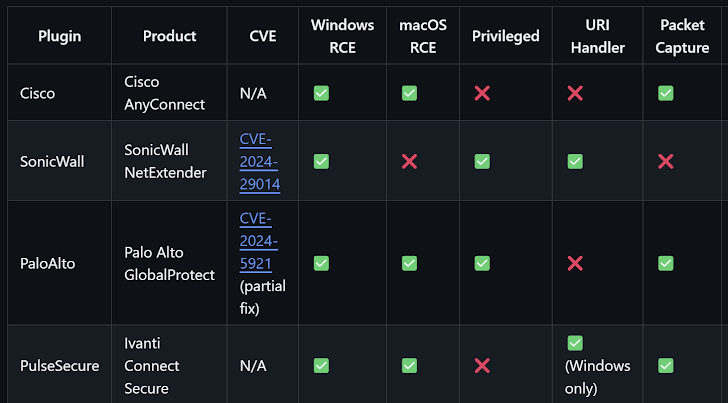
The identified flaws are listed below -
- CVE-2024-5921 (CVSS score: 5.6) - An insufficient certificate validation vulnerability impacting Palo Alto Networks GlobalProtect for Windows, macOS, and Linux that allows the app to be connected to arbitrary servers, leading to the deployment of malicious software (Addressed in version 6.2.6 for Windows)
- CVE-2024-29014 (CVSS score: 7.1) - A vulnerability impacting SonicWall SMA100 NetExtender Windows client that could allow an attacker to execute arbitrary code when processing an End Point Control (EPC) Client update. (Affects versions 10.2.339 and earlier, addressed in version 10.2.341)
Palo Alto Networks has emphasized that the attacker needs to either have access as a local non-administrative operating system user or be on the same subnet so as to install malicious root certificates on the endpoint and install malicious software signed by the malicious root certificates on that endpoint.
In doing so, the GlobalProtect app could be weaponized to steal a victim's VPN credentials, execute arbitrary code with elevated privileges, and install malicious root certificates that could be used to facilitate other attacks.
Similarly, an attacker could trick a user to connect their NetExtender client to a malicious VPN server and then deliver a counterfeit EPC Client update that's signed with a valid-but-stolen certificate to ultimately execute code with SYSTEM privileges.
"Attackers can exploit a custom URI handler to force the NetExtender client to connect to their server," AmberWolf said. "Users only need to visit a malicious website and accept a browser prompt, or open a malicious document for the attack to succeed."
While there is no evidence that these shortcomings have been exploited in the wild, users of Palo Alto Networks GlobalProtect and SonicWall NetExtender are advised to apply the latest patches to safeguard against potential threats.
The development comes as researchers from Bishop Fox detailed its approach to decrypting and analyzing the firmware embedded in SonicWall firewalls to further aid in vulnerability research and build fingerprinting capabilities in order to assess the current state of SonicWall firewall security based on internet-facing exposures.
North Korean Kimsuky Hackers Use Russian Email Addresses for Credential Theft Attacks
Cisco Warns of Exploitation of Decade-Old ASA WebVPN Vulnerability
Free online web security scanner






