Microsoft adds hotpatching support to Windows 11 Enterprise

Microsoft has announced that hotpatch updates are now available for business customers using Windows 11 Enterprise 24H2 on x64 (AMD/Intel) systems, starting today.
On devices where hotpatching is available, Windows allows users to install OS security updates by downloading and installing them in the background without rebooting the device.
To do that, it deploys the security updates by patching the in-memory code of running processes without restarting them after each installation.
"With hotpatch updates, you can quickly take measures to help protect your organization from cyberattacks, while minimizing user disruptions. You'll first create a hotpatch-enabled quality update policy in Windows Autopatch through the Microsoft Intune console," Microsoft said in a Wednesday message center update.
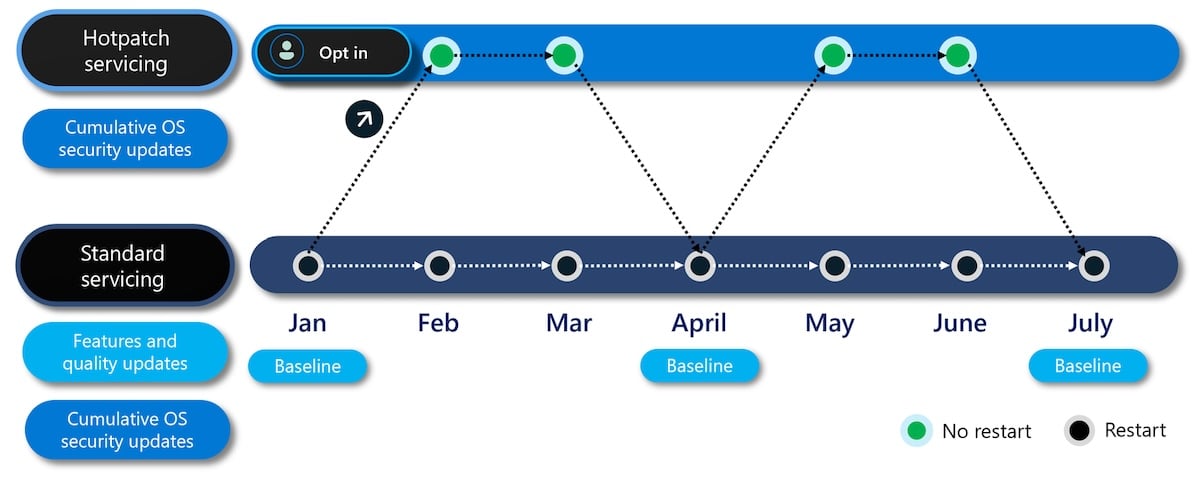
"Devices managed by this policy will be offered hotpatch updates in a quarterly cycle. Eight months out of twelve, you won't need to restart the device for the security update to take effect."
Eligible Windows 11 Enterprise 24H2 devices managed by this policy will be offered hotpatch updates quarterly, following the same ring deployment schedule as standard updates.
To enable hotpatching for Windows client devices, you will need a Microsoft subscription (i.e., Windows 11 Enterprise E3, E5, or F3, Windows 11 Education A3 or A5, or a Windows 365 Enterprise subscription) and a Windows 11 Enterprise 24H2 PC with the current baseline update installed.
Other requirements include an x64 AMD64 or Intel CPU, Virtualization-based Security (VBS) enabled, and Microsoft Intune to manage hotpatch update deployment with a hotpatch-enabled Windows quality update policy.
Microsoft says that hotpatch updates are still in public preview for Arm64 devices. However, admins can still turn off CHPE support by setting a HotPatchRestrictions registry key to ensure that these devices are eligible until the feature becomes available:
▪ Path: HKLM\SYSTEM\CurrentControlSet\Control\Session Manager\Memory Management
▪ DWORD Key value: HotPatchRestrictions=1If all prerequisites are met to receive hotpatch updates, you can enable or disable them by going to Devices > 'Windows updates'> 'Create Windows quality update policy' in the Microsoft Intune admin center to create a Windows quality update policy as shown in the screenshot embedded below.
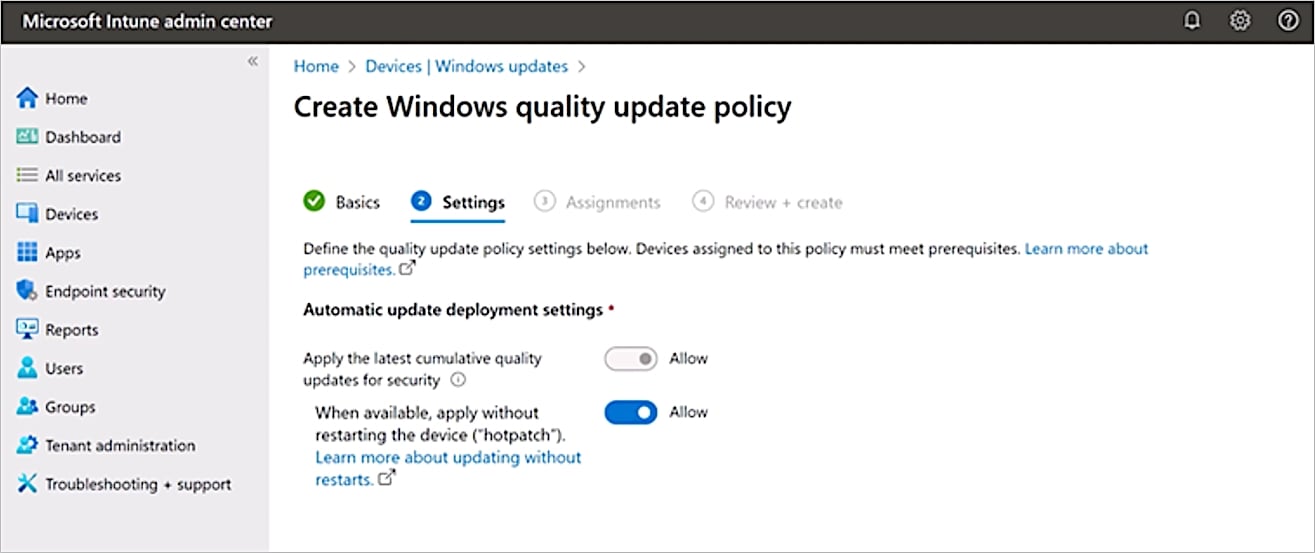
"The Windows quality update policy can auto-detect if your targeted devices are eligible for hotpatch updates," Microsoft added today.
"Devices running Windows 10 and Windows 11, version 23H2 and lower will continue to receive the standard monthly security updates, helping ensure that your ecosystem stays protected and productive."
Microsoft first added Windows Hotpatch support to Windows Server Azure Edition core virtual machines, making it generally available in February 2022 for systems running Windows Server 2022 Datacenter: Azure Edition.
The company also started testing it in public preview for Windows Server 2025 in September 2024 and on Windows 11 24H2 and Windows 365 two months later, in November 2024.
Top 10 MITRE ATT&CK© Techniques Behind 93% of Attacks
Based on an analysis of 14M malicious actions, discover the top 10 MITRE ATT&CK techniques behind 93% of attacks and how to defend against them.
Royal Mail investigates data leak claims, no impact on operations
GitHub expands security tools after 39 million secrets leaked in 2024
CVE-2025-22224 VMware ESXi and Workstation TOCTOU Race Condition Vulnerability
CVE-2025-2783 Google Chromium Mojo Sandbox Escape Vulnerability
CVE-2020-29574 CyberoamOS (CROS) SQL Injection Vulnerability
CVE-2022-43939 Hitachi Vantara Pentaho BA Server Authorization Bypass Vulnerability
CVE-2022-43769 Hitachi Vantara Pentaho BA Server Special Element Injection Vulnerability
CVE-2018-8639 Microsoft Windows Win32k Improper Resource Shutdown or Release Vulnerability
CVE-2024-40890 Zyxel DSL CPE OS Command Injection Vulnerability
CVE-2024-49035 Microsoft Partner Center Improper Access Control Vulnerability
CVE-2017-0148 Microsoft SMBv1 Server Remote Code Execution Vulnerability
InformationalUser Controllable JavaScript Event (XSS)
InformationalContent Security Policy (CSP) Report-Only Header Found
InformationalImage Exposes Location or Privacy Data
HighOpen Redirect
InformationalASP.NET ViewState Disclosure
Free online web security scanner







