Horns&Hooves Campaign Delivers RATs via Fake Emails and JavaScript Payloads
A newly discovered malware campaign has been found to target private users, retailers, and service businesses mainly located in Russia to deliver NetSupport RAT and BurnsRAT.
The campaign, dubbed Horns&Hooves by Kaspersky, has hit more than 1,000 victims since it began around March 2023. The end goal of these attacks is to leverage the access afforded by these trojans to install stealer malware such as Rhadamanthys and Meduza.
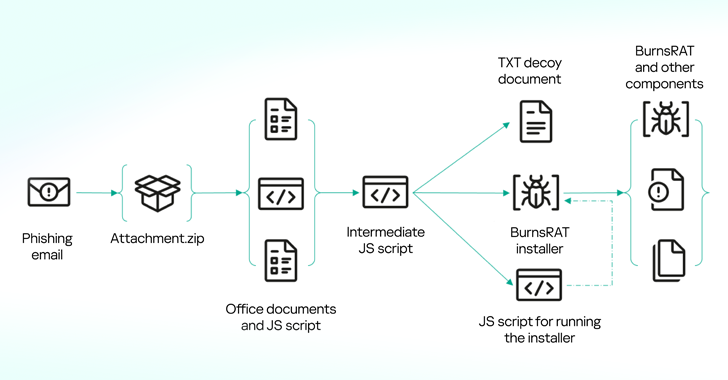
"Recent months have seen a surge in mailings with lookalike email attachments in the form of a ZIP archive containing JScript scripts," security researcher Artem Ushkov said in a Monday analysis. "The script files [are] disguised as requests and bids from potential customers or partners."
The threat actors behind the operations have demonstrated their active development of the JavaScript payload, making significant changes during the course of the campaign.
In some instances, the ZIP archive has been found to contain other documents related to the organization or individual being impersonated so as to increase the likelihood of success of the phishing attack and dupe recipients into opening the malware-laced file.
One of the earliest samples identified as part of the campaign is an HTML Application (HTA) file that, when run, downloads a decoy PNG image from a remote server using the curl utility for Windows, while also stealthily retrieving and running another script ("bat_install.bat") from a different server using the BITSAdmin command-line tool.
The newly downloaded script then proceeds to fetch using BITSAdmin several other files, including the NetSupport RAT malware, which establishes contact with a command-and-control (C2) server set up by the attackers.

A subsequent iteration of the campaign observed in mid-May 2023 involved the intermediate JavaScript mimicking legitimate JavaScript libraries like Next.js to activate the NetSupport RAT infection chain.
Kaspersky said it also found another variant of the JavaScript file that dropped an NSIS installer that's then responsible for deploying BurnsRAT on the compromised host.
"Although the backdoor supports commands for remotely downloading and running files, as well as various methods of executing commands via the Windows command line, the main task of this component is to start the Remote Manipulator System (RMS) as a service and send the RMS session ID to the attackers' server," Ushkov explained.
"RMS is an application that allows users to interact with remote systems over a network. It provides the ability to manage the desktop, execute commands, transfer files and exchange data between devices located in different geographic locations."
In a sign that the threat actors continued to tweak their modus operandi, two other attack sequences spotted in late May and June 2023 came with a completely reworked BAT file for installing NetSupport RAT and incorporated the malware directly within the JavaScript code, respectively.
There are indications that the campaign is the work of a threat actor known as TA569 (aka Gold Prelude, Mustard Tempest, and Purple Vallhund), which is known for operating the SocGholish (aka FakeUpdates) malware. This connection stems from overlaps in the NetSupport RAT license and configuration files used in respective activities.
It's worth mentioning that TA569 has also been known to act as an initial access broker for follow-on ransomware attacks such as WastedLocker.
"Depending on whose hands this access falls into, the consequences for victim companies can range from data theft to encryption and damage to systems," Ushkov said. "We also observed attempts to install stealers on some infected machines."
Korea arrests CEO for adding DDoS feature to satellite receivers
North Korean Kimsuky Hackers Use Russian Email Addresses for Credential Theft Attacks
Free online web security scanner






