Hackers Exploit Google Tag Manager to Deploy Credit Card Skimmers on Magento Stores
Threat actors have been observed leveraging Google Tag Manager (GTM) to deliver credit card skimmer malware targeting Magento-based e-commerce websites.
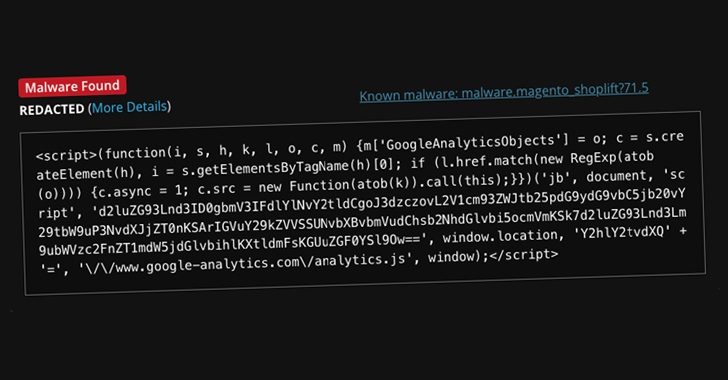
Website security company Sucuri said the code, while appearing to be a typical GTM and Google Analytics script used for website analytics and advertising purposes, contains an obfuscated backdoor capable of providing attackers with persistent access.
As of writing, as many as three sites have been found to be infected with the GTM identifier (GTM-MLHK2N68) in question, down from six reported by Sucuri. GTM identifier refers to a container that includes the various tracking codes (e.g., Google Analytics, Facebook Pixel) and rules to be triggered when certain conditions are met.
Further analysis has revealed that the malware is being loaded from the Magento database table "cms_block.content," with the GTM tag containing an encoded JavaScript payload that acts as a credit card skimmer.
"This script was designed to collect sensitive data entered by users during the checkout process and send it to a remote server controlled by the attackers," security researcher Puja Srivastava said.

Upon execution, the malware is designed to pilfer credit card information from the checkout pages and send it to an external server.
This is not the first time GTM has been abused for malicious purposes. In April 2018, Sucuri revealed that the tool was being leveraged for malvertising purposes.
The development comes weeks after the company detailed another WordPress campaign that likely employed vulnerabilities in plugins or compromised admin accounts to install malware that redirected site visitors to malicious URLs.
Free online web security scanner






