Hackers exploit DoS flaw to disable Palo Alto Networks firewalls

Palo Alto Networks is warning that hackers are exploiting the CVE-2024-3393 denial of service vulnerability to disable firewall protections by forcing it to reboot.
Leveraging the security issue repeatedly, however, causes the device to enter maintenance mode and manual intervention is required to restore it to normal operations.
"A Denial of Service vulnerability in the DNS Security feature of Palo Alto Networks PAN-OS software allows an unauthenticated attacker to send a malicious packet through the data plane of the firewall that reboots the firewall," reads the advisory.
DoS bug is actively exploited
Palo Alto Networks says that exploiting the vulnerability is possible by an unauthenticated attacker that sends a specially crafted, malicious packet to an affected device.
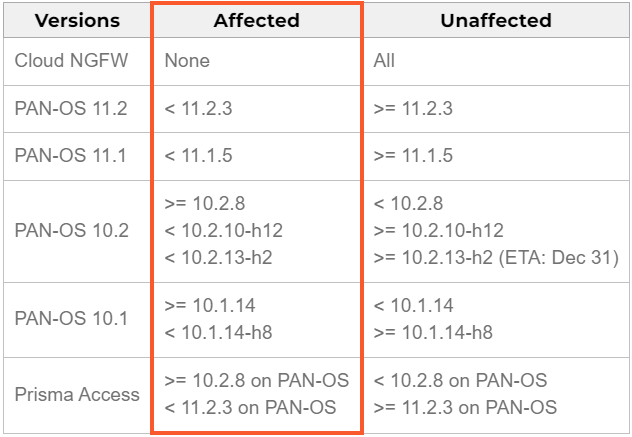
The issue only impacts devices where 'DNS Security' logging is enabled, while the product versions affected by CVE-2024-3393 are shown below.
The vendor confirmed that the flaw is actively exploited, noting that customers experienced outages when their firewall blocked malicious DNS packets from attackers leveraging the issue.
The company has addressed the flaw in PAN-OS 10.1.14-h8, PAN-OS 10.2.10-h12, PAN-OS 11.1.5, PAN-OS 11.2.3, and subsequent releases.
However, it's noted that PAN-OS 11.0, which is impacted by CVE-2024-3393, will not receive a patch because that version has reached its end-of-life (EOL) date on November 17.
Palo Alto Networks has also published workarounds and steps to mitigate the problem for those who cannot immediately update:
For unmanaged NGFWs, NGFWs managed by Panorama, or Prisma Access Managed by Panorama:
- Navigate to: Objects → Security Profiles → Anti-spyware → DNS Policies → DNS Security for each Anti-spyware profile.
- Change the Log Severity to "none" for all configured DNS Security categories.
- Commit the changes and revert the Log Severity settings after applying the fixes.
For NGFWs managed by Strata Cloud Manager (SCM):
- Option 1: Disable DNS Security logging directly on each NGFW using the steps above.
- Option 2: Disable DNS Security logging across all NGFWs in the tenant by opening a support case.
For Prisma Access managed by Strata Cloud Manager (SCM):
- Open a support case to disable DNS Security logging across all NGFWs in your tenant.
- If needed, request to expedite the Prisma Access tenant upgrade in the support case.
Cybersecurity firm's Chrome extension hijacked to steal users' data
North Korean Hackers Deploy OtterCookie Malware in Contagious Interview Campaign
Free online web security scanner






