CWE-1316 - Fabric-Address Map Allows Programming of Unwarranted Overlaps of Protected and Unprotected Ranges
- Abstraction:Base
- Structure:Simple
- Status:Draft
- Release Date:2020-12-10
- Latest Modification Date:2023-06-29
Weakness Name
Fabric-Address Map Allows Programming of Unwarranted Overlaps of Protected and Unprotected Ranges
Description
The address map of the on-chip fabric has protected and unprotected regions overlapping, allowing an attacker to bypass access control to the overlapping portion of the protected region.
Various ranges can be defined in the system-address map, either in the memory or in Memory-Mapped-IO (MMIO) space. These ranges are usually defined using special range registers that contain information, such as base address and size. Address decoding is the process of determining for which range the incoming transaction is destined. To ensure isolation, ranges containing secret data are access-control protected. Occasionally, these ranges could overlap. The overlap could either be intentional (e.g. due to a limited number of range registers or limited choice in choosing size of the range) or unintentional (e.g. introduced by errors). Some hardware designs allow dynamic remapping of address ranges assigned to peripheral MMIO ranges. In such designs, intentional address overlaps can be created through misconfiguration by malicious software. When protected and unprotected ranges overlap, an attacker could send a transaction and potentially compromise the protections in place, violating the principle of least privilege.
Common Consequences
Scope: Confidentiality, Integrity, Access Control, Authorization
Impact: Bypass Protection Mechanism, Read Memory, Modify Memory
Related Weaknesses
Ivanti VPN customers targeted via unrecognized RCE vulnerability (CVE-2025-22457)
Ivanti patches Connect Secure zero-day exploited since mid-March
Microsoft Warns of Tax-Themed Email Attacks Using PDFs and QR Codes to Deliver Malware
Texas State Bar warns of data breach after INC ransomware claims attack
Recent GitHub supply chain attack traced to leaked SpotBugs token
Attackers are leveraging Cisco Smart Licensing Utility static admin credentials (CVE-2024-20439)
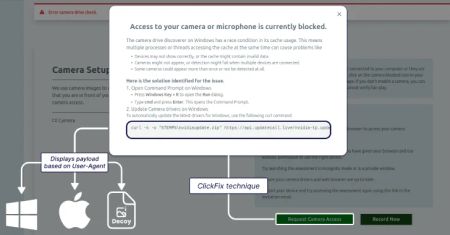
Lazarus Group Targets Job Seekers With ClickFix Tactic to Deploy GolangGhost Malware
AI Threats Are Evolving Fast — Learn Practical Defense Tactics in this Expert Webinar
AI Adoption in the Enterprise: Breaking Through the Security and Compliance Gridlock
CVE-2025-22224 VMware ESXi and Workstation TOCTOU Race Condition Vulnerability
CVE-2025-2783 Google Chromium Mojo Sandbox Escape Vulnerability
CVE-2020-29574 CyberoamOS (CROS) SQL Injection Vulnerability
CVE-2022-43769 Hitachi Vantara Pentaho BA Server Special Element Injection Vulnerability
CVE-2022-43939 Hitachi Vantara Pentaho BA Server Authorization Bypass Vulnerability
CVE-2018-8639 Microsoft Windows Win32k Improper Resource Shutdown or Release Vulnerability
CVE-2024-40890 Zyxel DSL CPE OS Command Injection Vulnerability
CVE-2024-49035 Microsoft Partner Center Improper Access Control Vulnerability
CVE-2017-0148 Microsoft SMBv1 Server Remote Code Execution Vulnerability
InformationalInformation Disclosure - Suspicious Comments
InformationalRe-examine Cache-control Directives