CWE-1290 - Incorrect Decoding of Security Identifiers
- Abstraction:Base
- Structure:Simple
- Status:Incomplete
- Release Date:2020-08-20
- Latest Modification Date:2023-06-29
Weakness Name
Incorrect Decoding of Security Identifiers
Description
The product implements a decoding mechanism to decode certain bus-transaction signals to security identifiers. If the decoding is implemented incorrectly, then untrusted agents can now gain unauthorized access to the asset.
In a System-On-Chip (SoC), various integrated circuits and hardware engines generate transactions such as to access (reads/writes) assets or perform certain actions (e.g., reset, fetch, compute, etc.). Among various types of message information, a typical transaction is comprised of source identity (to identify the originator of the transaction) and a destination identity (to route the transaction to the respective entity). Sometimes the transactions are qualified with a security identifier. The security identifier helps the destination agent decide on the set of allowed actions (e.g., access an asset for read and writes). A decoder decodes the bus transactions to map security identifiers into necessary access-controls/protections. A common weakness that can exist in this scenario is incorrect decoding because an untrusted agent's security identifier is decoded into a trusted agent's security identifier. Thus, an untrusted agent previously without access to an asset can now gain access to the asset.
Common Consequences
Scope: Confidentiality, Integrity, Availability, Access Control
Impact: Modify Memory, Read Memory, DoS: Resource Consumption (Other), Execute Unauthorized Code or Commands, Gain Privileges or Assume Identity, Quality Degradation
Related Weaknesses
Texas State Bar warns of data breach after INC ransomware claims attack
Recent GitHub supply chain attack traced to leaked SpotBugs token
Attackers are leveraging Cisco Smart Licensing Utility static admin credentials (CVE-2024-20439)
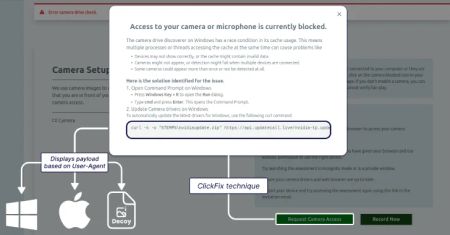
Lazarus Group Targets Job Seekers With ClickFix Tactic to Deploy GolangGhost Malware
AI Threats Are Evolving Fast — Learn Practical Defense Tactics in this Expert Webinar
AI Adoption in the Enterprise: Breaking Through the Security and Compliance Gridlock
Google Patches Quick Share Vulnerability Enabling Silent File Transfers Without Consent
Triada Malware Preloaded on Counterfeit Android Phones Infects 2,600+ Devices
Legacy Stripe API Exploited to Validate Stolen Payment Cards in Web Skimmer Campaign
CVE-2025-22224 VMware ESXi and Workstation TOCTOU Race Condition Vulnerability
CVE-2025-2783 Google Chromium Mojo Sandbox Escape Vulnerability
CVE-2020-29574 CyberoamOS (CROS) SQL Injection Vulnerability
CVE-2022-43939 Hitachi Vantara Pentaho BA Server Authorization Bypass Vulnerability
CVE-2022-43769 Hitachi Vantara Pentaho BA Server Special Element Injection Vulnerability
CVE-2018-8639 Microsoft Windows Win32k Improper Resource Shutdown or Release Vulnerability
CVE-2024-40890 Zyxel DSL CPE OS Command Injection Vulnerability
CVE-2024-49035 Microsoft Partner Center Improper Access Control Vulnerability
CVE-2017-0148 Microsoft SMBv1 Server Remote Code Execution Vulnerability
InformationalGraphQL Endpoint Supports Introspection
MediumAnti-CSRF Tokens Check
InformationalCookie Poisoning
LowStrict-Transport-Security Malformed Content (Non-compliant with Spec)
MediumFile Upload
HighCWE-77 Improper Neutralization of Special Elements used in a Command ('Command Injection')
CWE-1266 Improper Scrubbing of Sensitive Data from Decommissioned Device
CWE-303 Incorrect Implementation of Authentication Algorithm
HighCWE-650 Trusting HTTP Permission Methods on the Server Side
CWE-543 Use of Singleton Pattern Without Synchronization in a Multithreaded Context