CWE-1280 - Access Control Check Implemented After Asset is Accessed
- Abstraction:Base
- Structure:Simple
- Status:Incomplete
- Release Date:2020-02-24
- Latest Modification Date:2023-10-26
Weakness Name
Access Control Check Implemented After Asset is Accessed
Description
A product's hardware-based access control check occurs after the asset has been accessed.
The product implements a hardware-based access control check. The asset should be accessible only after the check is successful. If, however, this operation is not atomic and the asset is accessed before the check is complete, the security of the system may be compromised.
Common Consequences
Scope: Access Control, Confidentiality, Integrity
Impact: Modify Memory, Read Memory, Modify Application Data, Read Application Data, Gain Privileges or Assume Identity, Bypass Protection Mechanism
Related Weaknesses
Recent GitHub supply chain attack traced to leaked SpotBugs token
Attackers are leveraging Cisco Smart Licensing Utility static admin credentials (CVE-2024-20439)
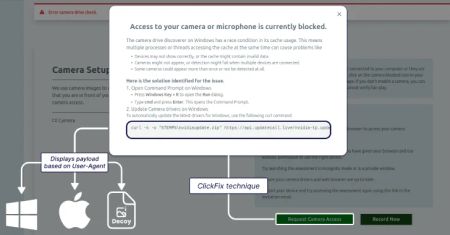
Lazarus Group Targets Job Seekers With ClickFix Tactic to Deploy GolangGhost Malware
AI Threats Are Evolving Fast — Learn Practical Defense Tactics in this Expert Webinar
AI Adoption in the Enterprise: Breaking Through the Security and Compliance Gridlock
Google Patches Quick Share Vulnerability Enabling Silent File Transfers Without Consent
Triada Malware Preloaded on Counterfeit Android Phones Infects 2,600+ Devices
Legacy Stripe API Exploited to Validate Stolen Payment Cards in Web Skimmer Campaign
Europol Dismantles Kidflix With 72,000 CSAM Videos Seized in Major Operation
Genetic data site openSNP to close and delete data over privacy concerns
CVE-2024-20439 Cisco Smart Licensing Utility Static Credential Vulnerability
CVE-2025-2783 Google Chromium Mojo Sandbox Escape Vulnerability
CVE-2019-9874 Sitecore CMS and Experience Platform (XP) Deserialization Vulnerability
CVE-2019-9875 Sitecore CMS and Experience Platform (XP) Deserialization Vulnerability
CVE-2025-30154 reviewdog/action-setup GitHub Action Embedded Malicious Code Vulnerability
CVE-2025-1316 Edimax IC-7100 IP Camera OS Command Injection Vulnerability
CVE-2024-48248 NAKIVO Backup and Replication Absolute Path Traversal Vulnerability
CVE-2017-12637 SAP NetWeaver Directory Traversal Vulnerability
CVE-2025-24472 Fortinet FortiOS and FortiProxy Authentication Bypass Vulnerability
InformationalInformation Disclosure - Suspicious Comments
InformationalRe-examine Cache-control Directives