CWE-1240 - Use of a Cryptographic Primitive with a Risky Implementation
- Abstraction:Base
- Structure:Simple
- Status:Draft
- Release Date:2020-02-24
- Latest Modification Date:2023-06-29
Weakness Name
Use of a Cryptographic Primitive with a Risky Implementation
Description
To fulfill the need for a cryptographic primitive, the product implements a cryptographic algorithm using a non-standard, unproven, or disallowed/non-compliant cryptographic implementation.
Cryptographic protocols and systems depend on cryptographic primitives (and associated algorithms) as their basic building blocks. Some common examples of primitives are digital signatures, one-way hash functions, ciphers, and public key cryptography; however, the notion of "primitive" can vary depending on point of view. See "Terminology Notes" for further explanation of some concepts. Cryptographic primitives are defined to accomplish one very specific task in a precisely defined and mathematically reliable fashion. For example, suppose that for a specific cryptographic primitive (such as an encryption routine), the consensus is that the primitive can only be broken after trying out N different inputs (where the larger the value of N, the stronger the cryptography). For an encryption scheme like AES-256, one would expect N to be so large as to be infeasible to execute in a reasonable amount of time. If a vulnerability is ever found that shows that one can break a cryptographic primitive in significantly less than the expected number of attempts, then that primitive is considered weakened (or sometimes in extreme cases, colloquially it is "broken"). As a result, anything using this cryptographic primitive would now be considered insecure or risky. Thus, even breaking or weakening a seemingly small cryptographic primitive has the potential to render the whole system vulnerable, due to its reliance on the primitive. A historical example can be found in TLS when using DES. One would colloquially call DES the cryptographic primitive for transport encryption in this version of TLS. In the past, DES was considered strong, because no weaknesses were found in it; importantly, DES has a key length of 56 bits. Trying N=2^56 keys was considered impractical for most actors. Unfortunately, attacking a system with 56-bit keys is now practical via brute force, which makes defeating DES encryption practical. It is now practical for an adversary to read any information sent under this version of TLS and use this information to attack the system. As a result, it can be claimed that this use of TLS is weak, and that any system depending on TLS with DES could potentially render the entire system vulnerable to attack. Cryptographic primitives and associated algorithms are only considered safe after extensive research and review from experienced cryptographers from academia, industry, and government entities looking for any possible flaws. Furthermore, cryptographic primitives and associated algorithms are frequently reevaluated for safety when new mathematical and attack techniques are discovered. As a result and over time, even well-known cryptographic primitives can lose their compliance status with the discovery of novel attacks that might either defeat the algorithm or reduce its robustness significantly. If ad-hoc cryptographic primitives are implemented, it is almost certain that the implementation will be vulnerable to attacks that are well understood by cryptographers, resulting in the exposure of sensitive information and other consequences. This weakness is even more difficult to manage for hardware-implemented deployment of cryptographic algorithms. First, because hardware is not patchable as easily as software, any flaw discovered after release and production typically cannot be fixed without a recall of the product. Secondly, the hardware product is often expected to work for years, during which time computation power available to the attacker only increases. Therefore, for hardware implementations of cryptographic primitives, it is absolutely essential that only strong, proven cryptographic primitives are used.
Common Consequences
Scope: Confidentiality
Impact: Read Application Data
Notes: Incorrect usage of crypto primitives could render the supposedly encrypted data as unencrypted plaintext in the worst case.
Related Weaknesses
Recent GitHub supply chain attack traced to leaked SpotBugs token
Attackers are leveraging Cisco Smart Licensing Utility static admin credentials (CVE-2024-20439)
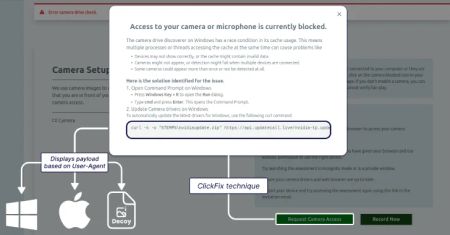
Lazarus Group Targets Job Seekers With ClickFix Tactic to Deploy GolangGhost Malware
AI Threats Are Evolving Fast — Learn Practical Defense Tactics in this Expert Webinar
AI Adoption in the Enterprise: Breaking Through the Security and Compliance Gridlock
Google Patches Quick Share Vulnerability Enabling Silent File Transfers Without Consent
Triada Malware Preloaded on Counterfeit Android Phones Infects 2,600+ Devices
Legacy Stripe API Exploited to Validate Stolen Payment Cards in Web Skimmer Campaign
Europol Dismantles Kidflix With 72,000 CSAM Videos Seized in Major Operation
Genetic data site openSNP to close and delete data over privacy concerns
CVE-2024-20439 Cisco Smart Licensing Utility Static Credential Vulnerability
CVE-2025-2783 Google Chromium Mojo Sandbox Escape Vulnerability
CVE-2019-9874 Sitecore CMS and Experience Platform (XP) Deserialization Vulnerability
CVE-2019-9875 Sitecore CMS and Experience Platform (XP) Deserialization Vulnerability
CVE-2025-30154 reviewdog/action-setup GitHub Action Embedded Malicious Code Vulnerability
CVE-2025-1316 Edimax IC-7100 IP Camera OS Command Injection Vulnerability
CVE-2024-48248 NAKIVO Backup and Replication Absolute Path Traversal Vulnerability
CVE-2017-12637 SAP NetWeaver Directory Traversal Vulnerability
CVE-2025-24472 Fortinet FortiOS and FortiProxy Authentication Bypass Vulnerability
InformationalInformation Disclosure - Suspicious Comments
InformationalRe-examine Cache-control Directives
CWE-543 Use of Singleton Pattern Without Synchronization in a Multithreaded Context
CWE-84 Improper Neutralization of Encoded URI Schemes in a Web Page
CWE-9 J2EE Misconfiguration: Weak Access Permissions for EJB Methods
CWE-1264 Hardware Logic with Insecure De-Synchronization between Control and Data Channels
HighCWE-732 Incorrect Permission Assignment for Critical Resource
CWE-180 Incorrect Behavior Order: Validate Before Canonicalize