CWE-106 - Struts: Plug-in Framework not in Use
- Abstraction:Variant
- Structure:Simple
- Status:Draft
- Release Date:2006-07-19
- Latest Modification Date:2023-06-29
Weakness Name
Struts: Plug-in Framework not in Use
Description
When an application does not use an input validation framework such as the Struts Validator, there is a greater risk of introducing weaknesses related to insufficient input validation.
Unchecked input is the leading cause of vulnerabilities in J2EE applications. Unchecked input leads to cross-site scripting, process control, and SQL injection vulnerabilities, among others. Although J2EE applications are not generally susceptible to memory corruption attacks, if a J2EE application interfaces with native code that does not perform array bounds checking, an attacker may be able to use an input validation mistake in the J2EE application to launch a buffer overflow attack.
Common Consequences
Scope: Integrity
Impact: Unexpected State
Related Weaknesses
Texas State Bar warns of data breach after INC ransomware claims attack
Recent GitHub supply chain attack traced to leaked SpotBugs token
Attackers are leveraging Cisco Smart Licensing Utility static admin credentials (CVE-2024-20439)
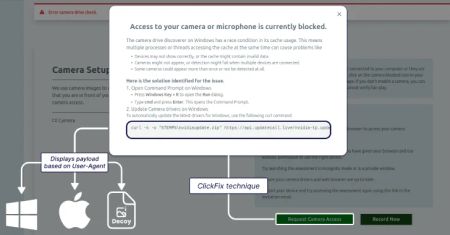
Lazarus Group Targets Job Seekers With ClickFix Tactic to Deploy GolangGhost Malware
AI Threats Are Evolving Fast — Learn Practical Defense Tactics in this Expert Webinar
AI Adoption in the Enterprise: Breaking Through the Security and Compliance Gridlock
Google Patches Quick Share Vulnerability Enabling Silent File Transfers Without Consent
Triada Malware Preloaded on Counterfeit Android Phones Infects 2,600+ Devices
Legacy Stripe API Exploited to Validate Stolen Payment Cards in Web Skimmer Campaign
CVE-2025-22224 VMware ESXi and Workstation TOCTOU Race Condition Vulnerability
CVE-2025-2783 Google Chromium Mojo Sandbox Escape Vulnerability
CVE-2020-29574 CyberoamOS (CROS) SQL Injection Vulnerability
CVE-2022-43939 Hitachi Vantara Pentaho BA Server Authorization Bypass Vulnerability
CVE-2022-43769 Hitachi Vantara Pentaho BA Server Special Element Injection Vulnerability
CVE-2018-8639 Microsoft Windows Win32k Improper Resource Shutdown or Release Vulnerability
CVE-2024-40890 Zyxel DSL CPE OS Command Injection Vulnerability
CVE-2024-49035 Microsoft Partner Center Improper Access Control Vulnerability
CVE-2017-0148 Microsoft SMBv1 Server Remote Code Execution Vulnerability
InformationalInformation Disclosure - Suspicious Comments
InformationalRe-examine Cache-control Directives